Hardware-Enforced Remote Access (HERA) – Under the Hood
Waterfall's Hardware-Enforced Remote Access is something new in the world - true interactive OT remote access with unidirectional protection for OT networks. How is this possible?
Andrew Ginter
HERA® - Big Picture
The big picture of HERA is similar to that of conventional, software-based remote access solutions:
In a highly automated mine, for example:
- A remote user – say a laptop is on a conference hotel’s Wi-Fi network remoting into the mine across the Internet,
- The HERA gateway is located at the protected mine site, and
- The protected OT network is “behind” the gateway – in this example the mining safety and other automation.
The big difference from conventional software-based remote access is what happens inside the HERA gateway.
“The big picture of HERA is similar to that of conventional, software-based remote access solutions….The big difference from conventional software-based remote access is what happens inside the HERA gateway.”
HERA Gateway
Under the hood of HERA are two instances of Waterfall’s flagship Unidirectional Security Gateways technology. One Unidirectional Gateway is oriented from the protected OT network out to the Internet-exposed IT network or to the Internet directly. That gateway’s hardware is physically able to send information in only one direction – the gateway sends HERA screen images out to the remote user across the Internet. Nothing can get back.
The second gateway under the hood of HERA is a variation of the standard Unidirectional Gateway. This gateway does two things. First, this second gateway sends HERA encrypted keystrokes and mouse movements (KMM) back into the OT network through the unidirectional hardware – nothing can get back out through that hardware. Second, the inbound hardware has gate array logic built in, and this logic scans the unidirectional communications and allows only the very simple encrypted HERA KMM information to pass – all other attempts at communication are rejected. Finally, on the OT network, that gateway’s receiving CPU runs virtual machine (VM) software, creating a brand new VM for each remote user session.
To recap, under the hood of the HERA gateway is:
- An inbound Unidirectional Gateway, which contains:
- An Internet-exposed CPU interacting with the remote user / laptop,
- One-way hardware that permits only encrypted KMM data to pass, and
- A CPU on the OT network receiving the encrypted KMM data, decrypting that data and sending keystrokes and mouse movements to the remote users’ session VMs,
- An Internet-exposed CPU interacting with the remote user / laptop,
- An outbound Unidirectional Gateway, which contains:
- A CPU on the OT network receiving screen images from the HERA VMs,
- One-way hardware,
- A CPU on the IT/Internet sending copies of HERA’s session VM screens across the Internet to remote users.
- A CPU on the OT network receiving screen images from the HERA VMs,
The whole solution fits in 2u of rack space.
A HERA Session
With that background, what does a HERA session look like? The remote user launches the HERA application on their desktop or laptop and chooses one of the configured destinations. This app runs only on computers equipped with a hardware-based Trusted Platform Module (TPM) and uses the TPM hardware to encrypt two (2) standard TLS connections to the HERA gateway. One connection sends encrypted KMM information, and the other receives screen images. The remote user sees the image of a VM screen come up, and the user is challenged for a username and password. This is in fact two-factor authentication, with the HERA encryption credentials stored in the laptop’s KVM hardware being the second form of authentication.
At this point, the user can move the mouse and type on the keyboard. The HERA app encrypts each keystroke and each mouse movement – this time using a different key in the TPM hardware. The app sends the encrypted KMM through the encrypted TLS connection into the HERA gateway.
Here’s the tricky part: the Internet-exposed CPU on the HERA gateway decrypts the TLS connection using its own TPM but does not have the keys to decrypt the encrypted KMM. So, the Internet-exposed CPU sends the encrypted KMM through the one-way hardware into the OT CPU in the HERA device. That OT CPU has the keys to decrypt the KMM and sends the decrypted KMM into the remote user’s virtual session. The virtual mouse moves. Keystrokes are used by the VM, and new screen images are sent back to the user.
How Secure Is this?
What does this mean security-wise? Well imagine that an attacker reaches across the Internet into the target’s IT network and uses a zero-day vulnerability to compromise both of the Internet-facing CPUs in the HERA gateway. What is the worst that can happen? Well, the attacker can interrupt the flow of screen images and KMM. But – can the attacker send arbitrary attack messages into the OT network to propagate the attack further into the network? No. The outbound gateway hardware lets nothing back in, and the HERA inbound gateway hardware lets only encrypted KMM messages back in. And if the attacker tries to forge keystrokes and mouse movements, it does not work – the compromised CPU does not have the keys to encrypt and authenticate keystrokes. Those keys are on the protected OT-resident CPU.
Contrast this with a firewall and software-based remote access solution. Exploit unpatched vulnerabilities in the firewall, VPN server or a complex remote access protocol server and we are in serious trouble. The attacker can reach through the compromised system software and send whatever messages they wish into the OT network to wreak havoc there. Yes, an attack on HERA’s Internet-exposed CPUs can cause the remote access solution to become inoperative, but at most sites this is an inconvenience, not a serious incident. At most sites, remote access saves a little money by reducing travel costs – remote access is generally not required to assure minute-by-minute correct operation of the industrial process.
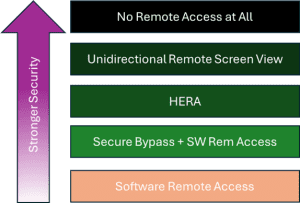
Bottom Line - a Spectrum of Security
Where does HERA fit within the broader spectrum of remote access solution security? In the illustration, HERA is positioned as stronger than software security, between Unidirectional Secure Bypass and Unidirectional Remote Screen View technologies:
- Conventional software-based remote access products at the bottom of the diagram have vulnerabilities, and rely on firewall software secure OT networks,
- Secure Bypass is a technology that temporarily enables bi-directional communications into a conventional software-based solution – Secure Bypass provides the OT site with local, physical control over when and how long remote users can access OT networks,
- HERA is hardware-enforced remote access,
- Unidirectional Remote Screen View makes copies of OT screen images out to external users through unidirectional hardware, while remote experts provide real-time feedback over the phone to engineers on site moving the mouse, and
- No remote access at all at the top of the illustration is the most secure option, but is also generally the most expensive option, because industrial sites are unable to take advantage of remote services and service providers.
The bottom line – HERA is something new in the world – the benefits of true interactive remote access without the risk that Internet-based attacks will use remote access vulnerabilities to attack OT targets.
For more details, please contact Waterfall to request a free consultation with a Waterfall HERA expert.
About the author
Andrew Ginter
Share
Trending posts
Webinar: 13 Ways To Break “Secure” OT Remote Access Systems
Webinar: 2026 OT Cyber Threat Report
Stay up to date
Subscribe to our blog and receive insights straight to your inbox