The unique circumstances surrounding 2+ years of a global pandemic, the war in Ukraine, and the recent uptick in attack sophistication has made this an auspicious time to better understand the state-of-play of OT cybersecurity programs. To this end, the folks at (CS)²AI, with the help of several Strategic Alliance Partners including Waterfall Security, have released the results of the 2nd annual survey of (CS)²AI’s industry members, the KPMG Control System Cyber Security Annual Report 2022. Waterfall supported the effort from survey design and results analysis to provide insights into the maturity and progress of OT security programs.
Just shy of 600 (CS)²AI industry members participated in the survey, the majority of whom are based in the US and Canada, and respondents consisted of professionals at all levels of their organizations. The responses reflect both the current state and longitudinal analysis (2020 to 2021) of topics concerning security events, attack activities, protective technologies, workforce readiness, and investment among others.
The past year has seen a sharp increase in high-profile OT cybersecurity incidents, dominating international headlines and putting control systems security front of mind for company leadership. As a result, the responses reveal significant changes year-on-year regarding cyber threat intelligence challenges, industrial security budget, network segmentation effectiveness, and the adoption of control systems cybersecurity technology such as unidirectional gateways. The myriad of findings reveals valuable takeaways about what the most mature and heavily invested sites are doing to protect critical systems.
One interesting approach taken by this survey was to look at the maturity level of the security programs in the respondents’ organizations. Respondents could identify themselves as Level 1 to 5 depending on the maturity of their security program. The responses were segregated between Low Maturity (1 or 2) and High Maturity (4 to 5) and provided insight as to the evolution of cybersecurity practices in organizations as they improve their security programs.
For example, concerning the use of frameworks (NIST, IEC62443, etc.), those organizations with higher maturity responded as using a great variety of frameworks, while organizations with lower maturity focused only on a small subset, particularly in the NIST Framework. A clear takeaway is that cybersecurity practices require a comprehensive look at different sources of expertise to provide a higher level of security.
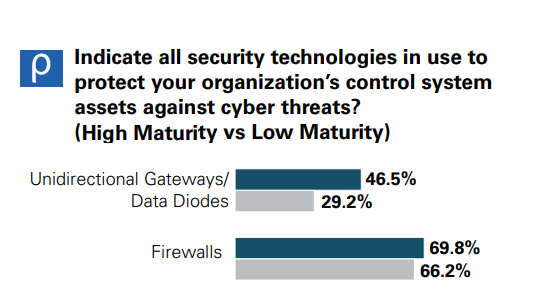 Another interesting takeaway observed is on the implementation of specific technologies in companies with high maturity vs. low maturity cyber security programs. The majority of respondents in the high maturity category implemented a defence-in-depth approach encompassing a suite of technologies including unidirectional gateways and intrusion detection systems. The respondents with high maturity security programs were 60% more likely to use unidirectional technologies compared to their low maturity counterparts.
Another interesting takeaway observed is on the implementation of specific technologies in companies with high maturity vs. low maturity cyber security programs. The majority of respondents in the high maturity category implemented a defence-in-depth approach encompassing a suite of technologies including unidirectional gateways and intrusion detection systems. The respondents with high maturity security programs were 60% more likely to use unidirectional technologies compared to their low maturity counterparts.
To dig deeper into other insights from this survey, please visit KPMG Control System Cyber Security Annual Report 2022.
Dig deeper – get the latest report now