USB Firmware Attack | Episode 120
Just imagine: You plug in a USB drive and your laptop starts smoking - nasty. Mario Prieto Sanlés of AuthUSB joins us to look at the nastiest of USB-based attacks, and what we can do about them.
Waterfall team

“…killer USB is is a commercial name for a device that kills the computer you connect it to. It sends 200 volts through the data lines and that completely burns the computer.”
About Mario Prieto Sanlés and AuthUSB
 Mario Prieto Sanlés is a pre-sales engineer at AuthUSB, a Spain-based company that sells hardware and software tools that physically protect computer networks and equipment from USB based threats. This includes protection against software attacks such as viruses and malware, hardware attacks such as Rubber Ducky, and electrical surge attacks such as Killer USBs, allowing total security when using USB devices.
Mario Prieto Sanlés is a pre-sales engineer at AuthUSB, a Spain-based company that sells hardware and software tools that physically protect computer networks and equipment from USB based threats. This includes protection against software attacks such as viruses and malware, hardware attacks such as Rubber Ducky, and electrical surge attacks such as Killer USBs, allowing total security when using USB devices.
Share
Transcript of this podcast episode #120:
USB Firmware Attacks
Please note: This transcript was auto-generated and then edited by a person. In the case of any inconsistencies, please refer to the recording as the source.
Nathaniel Nelson
Welcome. Everyone’s the industrial security podcast. My name is Nate Nelson I’m here with Andrew Ginter the vice president of industrial security at waterfall security solutions who’s going to introduce the subjects and guest of our show today Andrew how are you.
Andrew Ginter
I’m very well. Thank you Nate our guest today is Mario Prieto Sanles he is a solution architect at AuthUSB and we’re going to be looking at USB Firmware attacks and what we can do about them. These are not just you know. Open the USB drive and click on a malicious file and oops they got us these are attacks where the USB device itself is attacking us.
Nathaniel Nelson
Okay, then let’s get into it here is your interview with Mario.
Andrew Ginter
Hello mario and thank you for joining us before we get started. Can you tell us a few words about yourself and about the good work that you’re doing at AuthUSB.
Mario Prieto Sanles
Ah, hello Andrew thank you for invite me I’m Mario. I’m a Presales Engineer um Um I started. Um. Computer science engineer and also higer say hired technician on the Microcomputer systems and networks which we are focused on the cyber security systems. To provide protect our clients here now on our Csv we we contact the clients to prevent the company to be attacked with some different kinds of of malware attacks or also hardware attacks.
Andrew Ginter Thanks for that and you know you’ve used the word USB a couple of times I’ve used it a couple of times we all, you know, vaguely know what a USB is especially a USB thumb drive. Um, but we’re here talking about attacks. Um, why is USB a problem. How can you attack? anybody. Across a USB. What what sort of the the spectrum. What’s possible bad you know badness wise on a USB.
Thanks for that and you know you’ve used the word USB a couple of times I’ve used it a couple of times we all, you know, vaguely know what a USB is especially a USB thumb drive. Um, but we’re here talking about attacks. Um, why is USB a problem. How can you attack? anybody. Across a USB. What what sort of the the spectrum. What’s possible bad you know badness wise on a USB.
Mario Prieto Sanles
Okay, so for example, the FBI told us to prevent us to connect something to the USB and charging ports on the airport. For example because we can get infect our phone or our ipad or our whatever. Um, for example, we we can get in fact, connecting something to your computer a start us device are apparently a start us device you connect to to your computer and you get infected. Or. For example, you get your device killed by by the the device so there are many many ways to to attack your system. For example that killer USB is is a um, commercial name for a. you should be the device that kills the computer you connect it and it sends a 200 bolts through the data lines and that completely burns the computer so there are many many ways to get infected with the.
Mario Prieto Sanles
Electrical 3 the software 3 Or for example, the hardware thread that start injecting code in your machine so there are several ways to to attack your system with the USB devices.
Andrew Ginter
And so that’s interesting I might I’ve heard I’ve heard the word Killer USB before I thought I thought Killer USB was software some kind of software hack. You’re telling me it’s hardware?
Mario Prieto Sanles
Yeah, yeah, the killer USB is a so hard by that have electrical components built inside. They apparentlyly normal USB so when you connect to a computer and the killer USB chart dot electrical components and then send. 220 Volts through the dotline or maybe just 60 bolts through the data lines so it completely burns the computer. It seems like a lightning streak to your computer that burns the the power supply but in reality is ah. USB that kills the the motherboard and is use it to break the first layer of security and companies.
Nathaniel Nelson
you know I had some notion already that USBs could be dangerous. You know the classic You leave a USB in the parking lot. Someone picks it up brings it into their nuclear facility and it has stuxnet on it situation. But this thing where it delivers like voltage to kill a computer is I’ve never heard of anything in that ballpark.
Andrew Ginter
Um, yeah I had surprising you know I I thought I understood attack techniques. But this one is new to me so I did some reading afterwards and yeah apparentlyly the way it works is the device has capacitors in the USB drive. You plug it in and it starts drawing power I mean USB devices can do that you can draw power from these interfaces draws the power charges the capacitors and then discharges the capacitors at two hundred volts and fries your motherboard. So yeah and you know these devices are commercially available. You can buy them. Um, they’re not. Apparently illegal using them is illegal but the the device themselves isn’t illegal in theory their devices that manufacturers can use to test their Motherboards and and harden their motherboards you know in practice I don’t know any pen tester who does this I mean why would you go and burn out a dozen of your your clients. Computers. How can you do that with you know without consequences. But you know the reading I’ve done online does include a yeah, a caveat it says basically don’t do this at home kids.
Nathaniel Nelson
So has this kind of thing ever actually been pulled off by anybody
Andrew Ginter
Apparently you know one student did use a device like this. burned out sixty six zero computers at their school videoed themselves doing this and went to jail for a year.
Andrew Ginter
Ah, well, That’s nasty I mean I I really didn’t know that. Thank you? I had heard of the charging port Scenario I you know I dimly understand what’s happening there but you know you’re the expert on it. Can you tell us what’s happening under the hood in the airport. When one of these charging ports is compromised.
Mario Prieto Sanles
So the FBI told us we will not connect anything to to that charging ports because the so the the bad guys can change the fieldware of the of the charging port. The charging port is built with a. Chipset or a component that its name is a Bms is that ah, um, a company that controls the electricity that needs to be sent to the device. So they can change the behavior of that chipset to infect whatever is connected or for example, do you know? Um, but USB is is a commercial name of apparently.
Mario Prieto Sanles
Starts device but in reality is a chipset that sends data to the computer it it acts like a keyboard but physically isapp is is like a normal USB. So when you connect it. That but the USB to your computer you get infected by some script injected by but a cyber criminal.
Andrew Ginter
Yeah, so I’ve heard of bad USB before I thought you know you said you could buy it I thought bad USB was was open source was sort of a demonstration of you know for the for the penetration testers the demonstration of what’s what’s available for what what’s possible attack-wise.
Mario Prieto Sanles
Yeah, but the USB is is open source. You can build your own but you also can bite like a started kid with some threes some scripts that are already injected on the on that. But use video you you buy from the network. so there’s a lot of scripts already on. For example, github that you just need to follow a few steps to configure your bart USB in order to get for example passwords. Or inject. um, back door for the system or wherever there are already publish it on on github so you just need to download it.
Andrew Ginter
so bad USB I mean you know can you take us a little bit deeper. What is bad USB how does it work?
Mario Prieto Sanles
Okay, so when you’re go get the thumb drive a normal thumb drive you see a normal screen with the explorer of what’s inside what this is store stored on that thumb drivee. But when you connect by usv. You only see for example in in windows in windows system. Do you only see the console. Um, the console of the system that is injecting something but just a few seconds less than one second maybe that injects something. And that is living on your on your system. It’s a back door or a or a software that the service that is running in your computer. You only see a black screen for a little a little second one second maybe and and when it’s closed. And nothing’s happening. Nothing’s happening and and you only see foundraid connected but you don’t know what is happening. There are a lot of sophisticated and but usv with for example, a electrical component than a even a. First connection source explorer with the software inside. But when you connect later in the second connection. It sends the payload. It sends the um, the script injected on the on the computer.
Mario Prieto Sanles
So there are sophisticated sophisticated kinds of of bad use piece.
Nathaniel Nelson
Not sure if I missed some crucial bit of detail there but it sounds like what Mario’s describing is more along the lines of the kinds of USB attacks that I’m already aware of.
Andrew Ginter
Yeah I mean the the classic attack is one where there’s a nasty in the data of the USB drive. So I mean that was stuxnet the the structure of the the you know the the file system entries. In the USB drive itself confused the windows explorer exploited of vulnerability and and off you went the more conventional one is you know forget that kind of sophistication just put a nasty you know hackers r us xi on the USB and trick someone into double clicking. It. Yes I know it says hackers are us but that’s what you have to click click it now click there. You’re done. It’s over. You know that’s the contents’s you know’s there’s gigabytes tens of gigabytes of space on these devices if you fill it with malware and you trick someone or trick the computer into executing it. It’s all over this is a different attack. This is where you know every one of these USBs has a tiny little cpu in it people imagine it’s a device. It’s not a device. It’s a computer There’s a cpu in the USB device. It has its own software that little cpu is executing its own software. That’s called the firmware and normally the software. You know. You connect to the computer that the the computer inside the USB fires up and says hey I’m here I’m a you know a storage device. What do you want me to do and the computer says well you know, show me what’s in your you know what? what files you got and.
Andrew Ginter And it goes back and forth that way. There’s a conversation between the computer in the USB and and your computer. What’s happening here is the you connect it up and it says hey I’m a storage device and that conversation starts and the USB says by the way I’m also a keyboard. And it starts typing as if it were an external keyboard on your computer and it brings up a command window and starts typing into that window for a second or two you might catch it. You might be glancing away. You might not the window closes and it has injected a nasty into your computer.
And it goes back and forth that way. There’s a conversation between the computer in the USB and and your computer. What’s happening here is the you connect it up and it says hey I’m a storage device and that conversation starts and the USB says by the way I’m also a keyboard. And it starts typing as if it were an external keyboard on your computer and it brings up a command window and starts typing into that window for a second or two you might catch it. You might be glancing away. You might not the window closes and it has injected a nasty into your computer.
Nathaniel Nelson
We’re right.
Andrew Ginter
As if it had typed it from the keyboard.
Nathaniel Nelson
That seems so remarkable to me is there. No easy way for a computer to catch that kind of attack before it happens.
Andrew Ginter
Well, this is what we’re talking about. We’re describing the problem here. But you know we’re going to. We’re going to see the the solution in a minute This is what oth USB does.
Nathaniel Nelson
Yeah, okay, so basically though the lesson is that besides the the contents the files on USB drive. It’s the device itself too that you have to worry about trust with. So maybe you don’t accept a USB. On those grounds from anyone besides like a very trusted source.
Andrew Ginter
Yeah, it’s it’s worse than that actually um, you know there’s there’s stories out there. You know pen testers have published scenarios saying you got to be aware of this because we just did it to our client. The scenario was you know the pen testers were were tasked with getting into a heavily defended client. And they looked around and said you know we just can’t get in through this these people’s network. It’s it’s locked up tight. So what they did was one of these you know USB things they went out and purchased a very expensive mouse a very nice mouse carefully took the packaging apart. Carefully took the mouse apart inserted a USB drive into the mouse connected it all up to the the mouse’s USB put it all back together. Shrink-rapped the whole thing and sent it to you know one of the victims in in this the company they were testing. Um, so because they’d done some social media research they they figured out this person just came back from an expensive conference and said. Thank you for attending the conference here’s a thank you gift. You know, complete with the conference logo very official looking this person says. Lovely opens it up. Oh this is nice. This is a $200 mouse from my $3000 conference. Thank you plugs it in starts using it 12 hours later in the dead at night it says yes I’m a mouse I’m also a USB drive and you know.
Andrew Ginter
Window pops up and the mouse starts moving double clicks on the the the contents and now the computer is compromised so it’s not just USB drives that are at issue here if you’re given a gift of any USB device be deeply deeply suspicious of it.
-7:30
Andrew Ginter
So This is all nasty. Um, but you know this is the industrial security podcast. Can you talk about the industrial environment. I mean I see USBs everywhere I mean what? what should industrial users be worried about what should they be thinking about here?
Mario Prieto Sanles
Okay, so the best way to prevent an attack with USB devices is just don’t using them. Don’t use them so in ot environments in industrial environments.. They cannot do that they are they need to use USB devices because they have legacy devices where they cannot carry their update or or whatever. So um.
Mario Prieto Sanles
They need to use USB devices. They are forced to use a USB devices on old environments.
Andrew Ginter
Okay, so that’s all nasty. Um, how do we solve this problem I mean I see people using USBs at industrial sites because presumably they have to they have to load a Plc ladder logic program into the device and you know the the USB is the only way to do it. Um. How do they? How do? How do you address this problem.
Mario Prieto Sanles
So the only way you can get um, protect to through to these attacks is 3 checking 3 kinds of 3 the electrical one the hardware I one on the software attack. You need to check the behavior of the thumb drivee in order to detect these 3 kinds of 3 if you can get that your protect of every kind of attack with the USB protocol.
Andrew Ginter
Okay, so so there’s 3 things that we have to protect against we have to protect against the the you know the high voltage electrical Nasty. We have to do something about the hardware. Can you can you tell us you know what? what you guys do this? What do you guys? do when you say the words. Electrical hardware and software when you do this? What does it mean? What do you guys? actually do with your product.
Mario Prieto Sanles
Okay, so we develop a device a hardware device physical device which and detects the behavior of whatever is connected to our device. So if you connect a killer use via electrical feed when you connect it. We check the behavior and if if it breaks the USB protocol for stores the device we block it. We detect it. We block it. And we also report to the admin that someone someone is connecting Killer USB on the port number one in the in the device in the company or on the floor 3 or your company. So the idea is. To um, check the USB protocol that which is a which is a very strict the USB protocol said you need to do this in this exactlyly time. So if something is connected and don’t follow. strictly the USB protocol. It means that it’s talking with some other components is talking with or is typing.
Mario Prieto Sanles
Ah, to the computer or is charging the the electrical components to to send the bulge through the data lines. So It means it’s doing something else that needs to be needs to do if it was a store at The. startup device.
Andrew Ginter
Okay, so so you check the hardware if there’s over voltage. You know you you block that That’s great. Um, you’ve checked the.
Andrew Ginter
The USB protocol. It’s supposed to be a drive. It’s not supposed to be a keyboard when you say checking the protocol you’ve said electrical hardware and software is checking the protocol hardware software.
Mario Prieto Sanles
okay, so um, the electrical one is the killer use vita chairs. the electrical components and then send the the. Bolts through day times. The hardware attack is the rubber ducky the the bad USB with all the we talked and and then is the software that is this a kind of 3 the software thread is a completely normal sun drive. But with. Some software with some malware inside. So we check the USB protocol for for the two the the electrical we check the USB protocol for the electrical attack and we check the USB protocol for the hardware attack and we. Have antibios built inside on our device to check the software attack.
Andrew Ginter
Okay, and can you tell me I mean how does your device. What does it look like physically I mean is this something that I you know plug into the wall to have power and I put my USB in and it gives me a green light and says your USB is good. Go use it wherever you want and then I go plug the USB into the plc. Or do I plug your device into the plc and then plug the USB into your device is it between the USB and the and the Plc or is it is it sort of off on the side somewhere.
Mario Prieto Sanles
Okay, okay, so the our device is the it’s going to be the first layer of security or your company is a located on the first door of your industrial facilities. So when someone came to your industrial organization with with a thumb drivey. They go to the security, the security office. With the security guy he connect. um, the thumb drive to our solution and from our solution you can transfer the files to the net through the network. To your Vlc or to the shard folder you want to sfdp folder you want in order to get that files directly from our device without connecting that front drive that that sun drive.
Mario Prieto Sanles
To your computer and disposings yourselfs to a toid that changed the behavior for example in the at the second connection. So Our the device is connected to a power supply and and also with the ethernet a core. To your network.
-28:12
Nathaniel Nelson
Andrew I’m going to need a little bit of help here I follow how this device handles. You know, typical software threats right? He mentioned antivirus but how does it prevent the you know the USB that is going to fry my motherboard.
Andrew Ginter
And that’s just it. This is a separate physical device plugged into the wall. It does not prevent the USB frying your motherboard it detects so you stick the USB drive in there and you know it’s it’s going to give you a red flashing light saying whatever you do. Don’t plug this thing into the Plc it will fry your plc it detects rather than prevents.
Nathaniel Nelson
Okay, but then why doesn’t this USB fry the device itself that’s detecting this.
Andrew Ginter
Well, you know that’s the thing the the device is designed understanding that you know nasty stuff physically electrically could be coming at it. So it’s designed to withstand electrical abuse. You know you can design a circuit board for 200 volts you you know there’s there’s things you can do you just you have to know what’s coming at you and they’ve they’ve taken this into account you know and they so you know they they do detection. They do antivirus just like you said they do the electrical saying something electrical just happened and they do the the firmware detection as well. Really. You know what he said was look. We understand electrically you know voltage-wise and signalwise electrically what a normal USB drive behaves like it behaves at five volts we understand USB protocol-wise what a normal USB drive behaves like you send it this. Question it sends you back that answer you send it this other thing you you understand the USB protocol for a thumb drive and so what they’re doing is looking hard at what the USB is doing is it deviating from the electrical protocol with high voltage. Is it deviating. From the drive protocol by saying hey I’m a keyboard any deviation gives you a red light saying whatever you do do not plug this thing into your industrial network.
Nathaniel Nelson
Yeah, it also occurs to me now that you’re describing all of this that if were the USB to fry this device which as you mentioned it won’t because they’ve prepared for that that would be a pretty good detection mechanism in and of itself because they need to have a broken machine and then you’d probably not want to plug that USB in anywhere. Um. It kind of sounds like an advanced version of something we’ve talked about on pr episode. It’s the USB sanitation station where if you bring a device like that into a manufacturing plan or something you’ve got a plug in your USB there or else you’re not going to be allowed to use it elsewhere. But maybe like one or 2 extra steps involved.
Andrew Ginter
That’s exactly what it is I mean you’ve used the term sanitation station I’ve heard the term kiosk this is a physical device that sits at physical Security. You know you come into the the secure Zone.. In in the plant you’re asked to empty your pockets. Do you have any USBs stick all the USBs in the device. Um, you’re not allowed to carry the USBs into the the system. Anyway, it It takes the files off the system. Um, you know puts the files into the network. The clean ones that Antivirus has blessed. So yeah, this is this is a a kiosk. It’s a sanitation station. It. It lives as part of your physical security system sort of checking information and people and devices on the way into physically on the way into the the secure area.
Andrew Ginter
Okay, and so if I have a plc and the only way to change the latter logic is with a USB then what I have to do is take my sort of external USB. My suspect USB run it through your device.
Andrew Ginter
Get the files off of it on the other side and then you know inside the industrial network I need a bunch of I don’t know color coded USBs that have never touched the outside world I put the file back on one of those and I carry it over to the Plc is is that how it works.
Mario Prieto Sanles
Yeah, we we have several modes to to work with our product. we have an automatic mode for people who’s working on the factory that is only there for working not for knowing how to use. our product or other kinds of of products so we have a mode that automatically transfer everything from the external thumb drive to a internal thumb drive that is protected by you that is a. Inventory by by you this so is um, recognizable from the for the our product as known by our device.
Andrew Ginter
So that all makes sense. Um, can you give us some examples in the industrial space in your experience who is using these kind of products. What are they using them for um, you know are they finding anything?
Mario Prieto Sanles
Yeah, our main clients are a big companies with um, critical infrastructures also definite on the public infrastructures. Um.
Mario Prieto Sanles
They find attacks with a USB devices. and something that is important from our device is when you cannot check something. You are not. Knowing nothing about that about the tour of your company. For example, if you don’t have something that checks the email. You are not checking. If someone is downloading something from the from the email. So at this time nobody have nothing to control what is moving with the thumb stripes on your company. So.
Mario Prieto Sanles
Ah, first time. the first a day you connect our product. You start having everything that is running on the thunder drives on your company is and reported. In real time to a center console. So the admin can check everything that is running on thumb drives and from there we have clients that detect and someone is trying to inject the company with a bad USB. So that means that you are. Under attack because the you the about us we are a build specifically for you. There are no um, um, they they are built by a because of you they are built. specifically for you is it says strange to detect the bad USB that is not um, target to you so we detect and Killer USB with attack we have claims that the tax. A killer gb and then also bad USB the attack. The software attack is very very common. It. it’s normal to have a thumb drive that have so um, that have a malware a site. So.
Mario Prieto Sanles
The the most important is the most important to the tech. on the unblock and also report is the electrical and the hardware attacks.
Andrew Ginter
So that was a long answer. Let me let me summarize what I heard Mario say was that? yeah, their systems in in use and most of their customers are are you know large critical infrastructure sites. their systems have detected all 3 kinds of attacks. the most common attack that they detect is you know the stuff that the antivirus catches. There’s a nasty in you know so you know one of your files in the 600 files on the drive you know and quarantine. It. So that’s sort of commonplace. Um, he also said that the Killer USB the high voltage has been detected. In the wild which surprises me I would have thought that you know if that was going on in the wild. You’d hear more about it and you know this is the first I’ve heard of it so that’s a bit of a surprise. Um, he also said that the firmware attacks have been detected in the wild and these are in a sense particularly. Alarming because he says in in practice when they’ve been detected pretty much always they have identified a targeted attack meaning someone with a lot of resources put together. an attack that is specific. To this critical infrastructure site or that you know very valuable industrial site. You know who has those kinds of resources for that kind of investment in attack technology. It’s usually a nation state. So that’s disturbing that these have been discovered in the wild as well.
Nathaniel Nelson
Yeah, it strikes me that these kinds of attacks wouldn’t be cybercriminal in nature but also that I haven’t really heard about them before is there a reason why they wouldn’t make the news.
Andrew Ginter
Well um, you know you have to ask who’s detecting these attacks if it if it is nationst state. It may well be you know Nation State attacks on very sensitive targets. You know he did not say that they have I don’t know military customers If you’ve got a very sensitive target.
Andrew Ginter
And if you know let’s say a large government owned facility. Whatever kind of facility. It is you know they might just not report hey we think the russians or Iran or someone you know North Korea has just come after us. They might share that knowledge within you know their. They’re classified within their their their circle of of you know people that they they inform confidentially about these attacks to say you know here’s what’s happening protect yourself. Um, but you know if the man on the street is not at risk of you know a nation state coming after them.
Andrew Ginter
You know, maybe they figure they don’t need to know and the people who do need to know you know our allies have been informed through classified channels I don’t know I I don’t have a security clearance I never see any of this So this is all speculation on my part but it it seems plausible.
Andrew Ginter
So on the industrial side. Let’s let’s take a step back on the industrial side the USB attack everybody talks about is stuxnet a very sophisticated attack. You know nation-state grade how confident should we be of the auth USB solution could can you detect. You know that grade of of sophisticated attack.
Mario Prieto Sanles
Yeah, we are. um, we are confident on our solution. because of we check the the behavior but the confident that a client needs to to contact us. Is that we are thirtytified by our spanish cryptological center on. Also we are approved and also thirtytified. There’s 2 2 options here thirtytified or approved we are both. We are certified on approve to work with our spanish national cybersecur scheme and also we are certified to work with Nato nato countries. we um, we get through reverse engineer program in order to 35 and we are 100% made in Spain we don’t use electrical components from the front outside outside of the and european union so and.
Mario Prieto Sanles
That’s the confidence we and send to the to the our clients so that’s good. Um, you guys have been you know doing this for a while. Um. Can you give us any any view into the future I mean where where’s this going? What are you guys doing next.
Mario Prieto Sanles
Okay, so the the best thing we have today is a third besian we start this company. We started this company in 2018 This is the third version that we are working on the new persons with more ports. So the the model today have 2 ports through 2 version 3 of the USB protocol. and we are working on the different kinds of of devices. Everything to to attack USB attacks but different kinds of the devices with maybe a screen or we have more connectors. TypeC person to to to support the USBs with type c or we we are we are working on um, more than more than one the device more than one model.
Andrew Ginter
Well, this has been great Mario thank you for joining us before we let you go um, you know can you tell our listeners. What what should they be? What should they be taking away. What should they be watching in this USB space.
Mario Prieto Sanles
So. The first thing is never trust that USB the devices. It can look like a thumb drive like your fair your friends thumbrie but in reality it can be anything. It can be a um. keyboard you can be bluetooth connection or a wi-fi connection. So beware of um, beware of Thumb drive because it is it the the first. Seen the cyber criminal tries to do because it’s cheap and is is the first is the fastest way to to get inside your system. So um, the second thing you. need to know is our goods from the I would USB is that we we are focused on the those environments where they need to use USB devices every day for every action. And we are a um, checking the behavior we are the only ones that check the behavior of the USB devices other looks on the blacklist or white list. We. We just check the the behavior of whatever is connected.
Mario Prieto Sanles
And we also report everything in real time. So the admin of your company can can see everything in in in real time. So if you want to to know more about our solution you you can just contact us. With our website is out USB.net and and from there you can contact and know more about our solutions.
Nathaniel Nelson
All right? that seems to have concluded your interview with Mario Andrew do you have a final thought that you can take us out with.
Andrew Ginter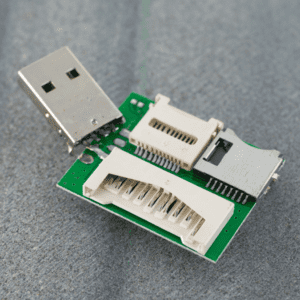 Yeah I mean something Mario said in sort of his sum up. Um, reminded me. you know we’ve talked about sort of in a sense the mundane the the normal the the kinds of attacks to expect? in. You know he reminded me that these kinds of attacks can become much more sophisticated imagine something that I mean these USB drives. They’ve got cpu’s inside they can be arbitrarily complicated. They can be arbitrarily powerful because they’re little computers imagine a USB drive that has a cpu inside. Yes. And I don’t know cellular hardware so it can reach out to the cellular network and say here I am what would you do with that. Well it would you know it could say to the the computer hey um, I’m a drive great I’m also a keyboard I’m also a mouse I’m also a screen and. You know what’s the default behavior on most windows computers when when it says hey I’m um, another screen it mirrors the first screen to the second screen and now you’ve got you’re seeing a copy of the screen you can move the mouse you can type in the keyboard this is nasty but you know all over the internet all by remote control. Um. You know the the bottom line here is that you know we need to be deeply suspicious of any USB drive that comes into our industrial network from the outside world. We need to scan it 9 ways to Sunday you know on.
Yeah I mean something Mario said in sort of his sum up. Um, reminded me. you know we’ve talked about sort of in a sense the mundane the the normal the the kinds of attacks to expect? in. You know he reminded me that these kinds of attacks can become much more sophisticated imagine something that I mean these USB drives. They’ve got cpu’s inside they can be arbitrarily complicated. They can be arbitrarily powerful because they’re little computers imagine a USB drive that has a cpu inside. Yes. And I don’t know cellular hardware so it can reach out to the cellular network and say here I am what would you do with that. Well it would you know it could say to the the computer hey um, I’m a drive great I’m also a keyboard I’m also a mouse I’m also a screen and. You know what’s the default behavior on most windows computers when when it says hey I’m um, another screen it mirrors the first screen to the second screen and now you’ve got you’re seeing a copy of the screen you can move the mouse you can type in the keyboard this is nasty but you know all over the internet all by remote control. Um. You know the the bottom line here is that you know we need to be deeply suspicious of any USB drive that comes into our industrial network from the outside world. We need to scan it 9 ways to Sunday you know on.
Andrew Ginter
The way into the network ideally pulling the you know the the contents off of it. Not allowing the physical device into the network at all. Um, so yeah, it’s it’s a modern threat. It’s you know? Thank you to Mario for reminding us of of this nasty attack pathway.
Nathaniel Nelson
Yes, thank you to Mario Sanles for speaking with you Andrew and Andrew thank you as always for speaking with me this has been the industrial security podcast from Waterfall. Thanks to everyone out there listening.
aginter
It’s always a pleasure. Thank you Nate.
Trending posts
Stay up to date
Subscribe to our blog and receive insights straight to your inbox