Content Category: Blog
Welcome to the resources page! We have compiled a collection of useful information, tools, and resources to help you
Secure Industrial Remote Access Solutions
Secure, efficient, and reliable industrial remote access solutions enable monitoring, maintenance, and troubleshooting of SCADA and control systems from anywhere, protecting critical operations.

SCADA Security Fundamentals
Protect SCADA systems with best practices in SCADA security, including access control, monitoring, encryption, and compliance for critical infrastructure.

What is OT Network Monitoring?
How OT network monitoring enhances industrial system security and reliability through real-time visibility, alert management, and tailored solutions for operational technology challenges.
What Is ICS (Industrial Control System) Security?
How ICS security protects Industrial Control Systems, from SCADA and PLCs to critical infrastructure, vulnerabilities, and best practices
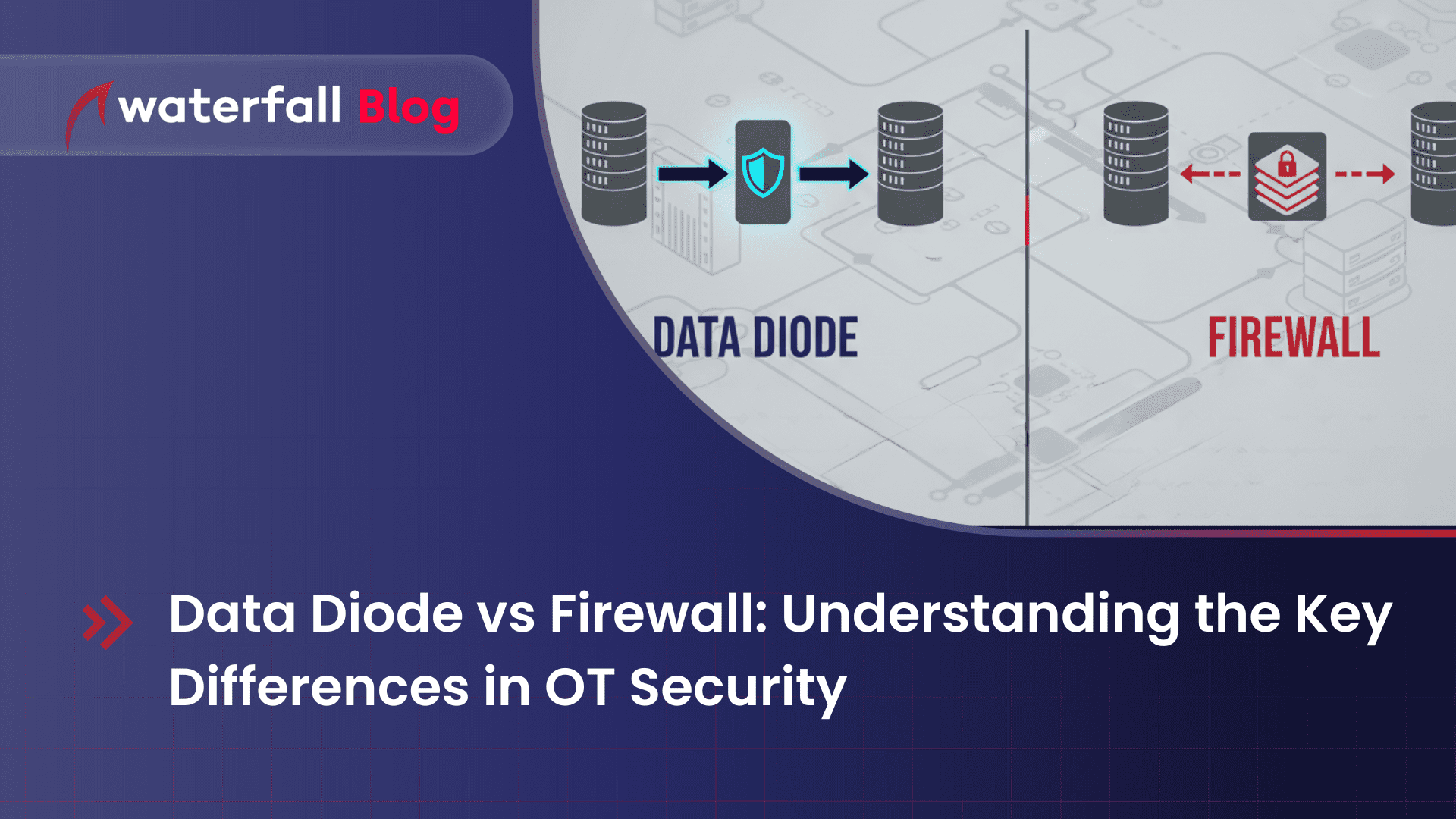
Unidirectional vs Bidirectional: Complete Integration Guide
Discover the key differences between unidirectional and bidirectional integration to choose the best approach for secure and efficient system connectivity.